Jun 03, 2020 Download Hacker Theme Pack For Windows 10. Top 4 Best Mac OS Theme Packs For Windows 10. Which Dock App are you choosing? I hope you have enjoyed the choices above for the best Mac OS Docks for Windows 10 2020. This will make your PC look and feel just like a MAC with the dock apps that you can download. Resource Hacker by Angus Johnson is a free-to-use resource editing application that can open and edit the data inside executable files. Even if there is no version of Resource Hacker for Mac available for download, you can try using other tools to complete this task. Jun 22, 2020 Apple has announced the all new iOS 14. And as always the company has added some iconic official iOS 14 wallpapers that will ship with the software update in the fall. If you haven’t downloaded the iOS 14 beta on your device but still want to. Hello everyone and welcome to our YouTube tutorial on Asphalt 8 Hack Tool For Windows 10 Pc! As of 2019 it is WORKING, with NO HUMAN VERIFICATION OR DOWNLOADING APPS (except for the first time), and OPTIONAL DOWNLOAD (you can also use it online). Jan 12, 2020 Dracos is built to be fast, strong, and powerful OS which is used to perform security testing (penetration testing). Powered by hundreds of pentest tools including information gathering, forensics, malware analysis, maintaining access, and reverse engineering, Dracos Linux is one of the best choices of hacker’s operating system.
- Better Touch Tool Mac Os
- Best Mac Tools
- Pro Tools Mac Os Catalina
- Mac Network Tools
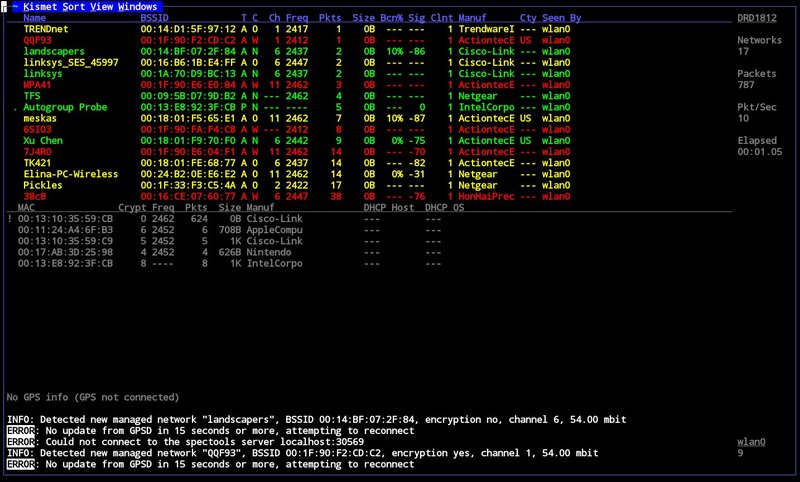
- Wifi Hacking Tools For Macos
- Vmware Tools Mac Os
Content Written By Henry Dalziel, 2020
Web Vulnerability Scanners For Use In 2020
Web Applications are hugely attractive to hackers and for a million different reasons not least because when they are mismanaged and unpatched then they suddenly become very easy to attack. What we’ve done in this resource is to list a bunch of Web Application Hacking Software that would be able to penetrate and pwn a Website (for example).
In order of priority, we note that these are the most popular Content Management Systems being used today.
- WordPress 28.6%
- Joomla 3.3%
- Drupal 2.3%
- Magneto 1.1%
- Blogger 1.0%
- Shopify 0.8%
So, clearly, with WordPress being the Internet’s #1 most popular CMS there is little doubt nor lack of evidence which shows just how many hackers go after WordPress.
WordPress hacking software is therefore plentiful and in this resource, we try to outline a bunch of tools and software that will help identify how secure your CMS really is.
Acunetix WVS
Acunetix is a web vulnerability scanner that automatically checks web applications. This tool is particularly good at scanning for vulnerabilities such as cross-site scripting, SQL injections, weak password strength on authentication pages and arbitrary file creation. It has a great GUI that has the ability to create compliance reports, security audits, and tools for advanced manual web app testing.
Is Acunetix WVS Free?
It is a commercial program but it’s fast and cheap.
Does Acunetix WVS Work on all Operating Systems?
It currently works on Windows operating systems.
What are the Typical Uses for Acunetix WVS?
Acunetix WVS is used to discover if your website is secure by crawling and analyzing your web applications to find if there are SQL injections. By doing this, its detailed report can identify where web applications need to be fixed.
AppScan
AppScan gives security testing throughout the application development lifecycle.
This tool can also assist with security assurance early in the development phase and easing unit testing. This tool can scan for many common vulnerabilities such as HTTP response splitting, cross-site scripting, hidden field manipulation, parameter tampering, buffer overflows, backdoors/debug options and many more.
Is AppScan Free?
The commercial version of this tool is available. Free trial versions might also be offered.
Does AppScan Work on all Operating Systems?
It only works on Microsoft Windows operating systems.
What are the Typical Uses for AppScan?
AppScan is used to the enhanced mobile application and web application security. It is also used to strengthen regulatory compliance and improve application security program management. This tool will also help users in identifying security vulnerabilities, generate reports and fix recommendations.
Burp Suite
Burp Site is a platform that contains different kinds of tools with many interfaces between them that are designed to facilitate and speed up processes of attacking applications.
Better Touch Tool Mac Os
All these tools share the same framework for displaying and handling HTTP messages, authentication, persistence, logging, alerting, proxies and extensibility.
Is Burp Suite Free?
A paid version is available. Free/trial versions may also be available.
Does Burp Suite Work on all Operating Systems?
Burp Suite Works on Linux, MAC OS X, and Windows operating systems.
What are the Typical Uses for Burp Suite?
This tool is used primarily to attack pentest web applications. It can also be used to read web traffics. Not only this app is useful and reliable. It also offers a lot of features.
Nikto
An open-source web server scanner, Nikto performs tests for over 6700 potentially dangerous files and programs on web servers.
It is also designed to check for over 1250 outdated server versions and specific version problems on over 2700 servers. Aside from that, it also checks server configuration items like the presence of multiple index files, HTTP server options and it will try to identify installed software and web servers. Plugins and scan items are frequently and can be automatically updated.
Although it is not designed to be a stealthy tool, it can test web servers in the fastest time possible. Nonetheless, there is also support for LibWhisker’s anti-IDS methods in case you want to try it by testing your IDS system for example.
Not all checks are security problems but security engineers and webmasters sometimes are not aware of the “info only” type of checks are present on their server. By using Nikto , these “info type” checks are marked in the information printed appropriately. Some check is also being scanned for unknown items in log files.
Is Nikto Website Vulnerability Scanner Free?
Yes, this tool is free to use and in fact, a lot of pentesters like this tool a lot.
Does Nikto Website Vulnerability Scanner Work on all Operating Systems?
Since Nikto is a perl based security testing tool, it will run on most systems with Perl interpreter installed.
What are the Typical Uses for Nikto Website Vulnerability Scanner?
Even if this scanner is free, it still has a lot of uses. Some of the uses include SSL Support, full HTTP proxy support, checking of outdated server components, save reports in various formats like XML, HTML, CSV or NBE, easily customize reports by using Template Engine, multiple ports scanning on a server or multiple servers via input file, identifies the software installed via header, files and favicons, host authentication with NTLM and Basic, checking of common “parking” sites, auto-pause at a specific time and a lot more….
Netsparker
We’ve covered this tool throughout our site on several occasions.
Rather than duplicate the content we recommend that you hit this link for detailed information and more resources on this tool.
OWASP Zed Attack Proxy
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools for scanning web applications.
This hacking tool is actively maintained by hundreds of international volunteers. It can help you automatically find security vulnerabilities in your web applications while you are developing and testing your applications. It’s also a great tool for experienced pentesters to use for manual security testing.
BeEF
Browser Exploitation Framework (Beef) is another great professional security tool. This tool will give the experienced penetration tester pioneering techniques.
Unlike other tools, Beef focuses on leveraging browser vulnerabilities to check the security posture of a target. This tool is created solely for penetration testing and lawful research.
Is Beef Free?
Beef is free to use.
Does Beef Work on all Operating Systems?
Beef is available for Windows, Linux, and Mac OS X operating systems.
What are the Typical Uses for Beef?
This tool that can demonstrate the collecting of browser vulnerabilities or zombie browsers in real-time. It gives a control and command interface which facilitates the targeting of groups or individuals of zombie browsers. It is built to make the creation of new exploit modules easy.
Core Impact
Core Impact is considered to be the greatest exploitation tool available.
It has a huge and regularly updated database of exploits and can do neat tricks like exploiting one computer system than building an encrypted tunnel through that system to reach and exploit other machines.
Is Core Impact Free?
No, and this tool is expensive (about $30,000).
Does Core Impact Work on all Operating Systems?
Core Impact is natively working on Microsoft Windows.
What are the Typical Uses for Core Impact?
With this tool, users can: Leverage true multi-vector testing capabilities across network, web, mobile, and wireless. Run and check for a high level of unique CVEs (in some cases more than other multi-purpose tools) and validate patching efforts to ensure vulnerabilities were remediated correctly.
Dradis
Dradis Framework is an open-source tool that enables users to have effective information and data sharing especially during security assessments. Features include an easy report generation, attachment support, integration with existing systems and tools through server plugins and platform-independent.
Is Dradis Free?
Dradis is free.
Does Dradis Work on all Operating Systems?
Dradis is compatible with Linux, MAC OS X, and Windows operating systems.
What are the Typical Uses for Dradis?
Dradis is used to enable effecting the sharing of information or data among participants in a penetration test. Dradis is also a self-contained web tool that gives a centralized repository of data to keep track of what has been done and what is still ahead.
Metasploit
Metasploit is a very popular hacking framework with hundreds (if not thousands) of scripts that you can use to find and progress with your hack. We’ve already covered this tool on our site and we’d encourage you to visit this link here for more details.
Social Engineer Toolkit
Written by the founder of TrustedSec, Social-Engineer Toolkit (SET) is an open-source Python-based tool aimed at penetration testing around Social Engineering.
SET has been discussed and presented at conferences including DerbyCOn, Defcon, ShmooCon, and Blackhat. This tool has over two million downloads, this engineering toolkit is the standard for penetration tests and is support by the security community. SET has also been featured in a number of books such as “Metasploit: The Penetration’s Tester’s Guide” that is also written by TrustedSec’s founder as well as Devon Kearns, Jim O’Gorman, and Mati Aharoni.
Is the Social-Engineer Toolkit Free?
Yes, all official versions are free of use.
Does Social-Engineer Toolkit Work on all Operating Systems?
SET works on Linux, MAC OS X, and Microsoft operating systems.
What are the Typical Uses for Social-Engineering Toolkit?
The main purpose of the set is to improve and automate a lot of the social engineering attacks out there. This tool can automatically generate exploit hiding email messages or web pages.
sqlmap
sqlmap is an open-source tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It includes a powerful detection engine, a lot of niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
Is Sqlmap free?
Yes, sqlmap is free to use and works out of the box with Python version 2.6.x and 2.7.x on any platform
1. Fully support MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, HSQLDB and Informix database management systems.
2. Fully support for 6 SQL injection techniques which are boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band.
3. It contains support to directly connect to the database without passing via a SQL injection, by providing DBMS credentials, IP address, port, and database name.
4. Contains support to enumerate users, password hashes, privileges, roles, databases, tables, and columns.
5. Contains an automatic recognition of password hash formats and support for cracking them using a dictionary-based attack.
6. Contains support to dump database tables entirely, a range of entries or specific columns as per user’s choice. The user can also choose to dump only a range of characters from each column’s entry.
7. Contains support to search for specific database names, specific tables across all databases or specific columns across all databases’ tables. This is useful, for instance, to identify tables containing custom application credentials where relevant columns’ names contain string like name and pass.
8. Contains support to download and upload any file from the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
9. Contains support to execute arbitrary commands and retrieve their standard output on the database server underlying operating system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
10. Contains support to create an out-of-band stateful TCP connection between the attacker machine and the database server underlying operating system. This channel can be an interactive command prompt, a Meterpreter session or a graphical user interface (VNC) session as per user’s choice.
11. Contains support for database process’ user privilege escalation via Metasploit’s Meterpreter getsystem command.
Some options for python sqlmap.py
Helpful Stuff
-h, –help Show basic help message and exit-hh Show advanced help message and exit–version Show program’s version number and exit-v VERBOSE Verbosity level: 0-6 (default 1) Target: At least one of these options has to be provided to define the target(s) -d DIRECT Connection string for direct database connection -u URL, –url=URL Target URL (e.g. “http://www.site.com/vuln.php?id=1”) -l LOGFILE Parse target(s) from Burp or WebScarab proxy log file -x SITEMAPURL Parse target(s) from remote sitemap(.xml) file -m BULKFILE Scan multiple targets given in a textual file -r REQUESTFILE Load HTTP request from a file -g GOOGLEDORK Process Google dork results as target URLs -c CONFIGFILE Load options from a configuration INI file
What are the Typical Uses for sqlmap?
Sqlmap is written in python and is considered as one of the most powerful and popular sql injection automation tool out there. Given a vulnerable http request url, sqlmap can exploit the remote database and do a lot of hacking like extracting database names, tables, columns, all the data in the tables etc. This hacking tool can even read and write files on the remote file system under certain conditions. sqlmap is like Metasploit of sql injections.
How To Install Sqlmap?
This tool works best on Linux, preferably something like Kali Linux, Backbox or any other flavours therein for Pentesting Purposes.
Step 1: sqlmap -u “http://www.yourwebsiteurl.com/section…(without quotation marks)” –dbs
Step 2: sqlmap -u “http://www.yourwebsiteurl.comsection….(without quotation marks)” -D database_name –tables
Step 3: sqlmap -u “http://www.yourwebsiteurl.com/section…(without quotation marks)” -D database_name -T tables_name –columns
Step 4: sqlmap -u “http://www.site.com/section.php?id=51(without quotation marks)” -D database_name -T tables_name -C column_name –dump
sqlninja
SQL Ninja enables users to exploit web applications that use a Microsoft SQL Server as its database backend.
It focuses on getting a running shell on a remote host. This tool automates the exploitation process once an SQL injection has been discovered.
Is SQL Ninja Free?
Yes! all versions of this tool are free of charge.
Does SQL Ninja Work on all Operating Systems?
SQL Ninja works on Linux and Mac OS X operating systems.
What are the Typical Uses for SQL Ninja?
This tool is best used by cyber professionals to assist in automating the process of taking over a database server when a SQL Injection vulnerability has been discovered. If you are interested in this tool then you should go ahead and also take a look at SQL Map.
w3af
w3af is one of the most popular, flexible and powerful tools for finding and exploiting web application vulnerabilities.
It is very easy to use and it offers dozens of features of exploitation and web assessment plugins. Others call it a web-focused Metasploit. w3af is divided into 2 main parts which are the core and the plugins. Plugins are categorized into different types and these are discovery, bruteforce, audit, evasion, grep, Attack, output and mangle.
Is w3af Free?
All versions of this tool are free.
Does w3af Work on all Operating Systems?
It works on Windows, Linux and Mac OS X operating systems.
What are the Typical Uses for w3af?

The use of this goal is to create a framework that will help users secure web applications by discovering and exploiting all web application vulnerabilities.
What is password cracking?Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes. When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking ToolsGiven below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
Features of Cain & Abel:- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
Features of John the Ripper- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
Features of Aircrack- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.
Features of THC Hydra- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/5. RainbowCrack : New Innovation in Password Hash Cracker

RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
Features of Rainbow Crack- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
Features of OphCrack- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.
Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks.
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
Best Mac Tools
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Pro Tools Mac Os Catalina
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
Mac Network Tools
Features of Medusa
Wifi Hacking Tools For Macos
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Vmware Tools Mac Os
Site for Download: